Facilitating a ransomware payment enables criminals to profit from their illicit activities and could violate OFAC regulations.
Author: Certitude Security
Intellectual Property Protections
The theft of vital or sensitive business secrets occurs daily. Protecting intellectual property should be one of your top priorities to ensure competitive advantage.
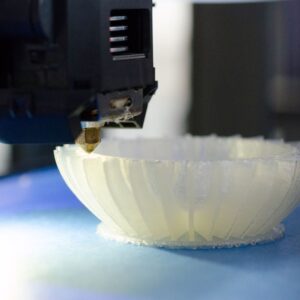
3D Printing in U.S. Manufacturing
3D printing or additive manufacturing has become popular in recent years, and many security experts have begun to express their concerns.
How does cyber security work, and what does it mean for businesses?
How does cyber security work in real-world contexts, & which steps should organizations take to establish a sustainable security posture? Learn more on the blog.
The Importance Of Cyber Security In Business
Responsibilities have moved to the board room because data breach factors that impact your bottom line are not limited to revenue loss, damage to reputation, or loss of Intellectual Property.
5 Mistakes Executives Make Delegating Security To MSPs
MSPs claim to provide effective data security, so you delegate. You cannot relinquish responsibility and must inspect the work they perform. Trusting cybersecurity to your MSP is prone to problems that lead to disastrous results.
How to detect and mitigate cyber threats: Protecting your business in the digital age
How can you best protect your business in the digital age? Our blog walks through top cyber security threats, prevention, detection & more. Keep reading!
What is Social Engineering?
Given the financial losses due to the volume of social engineering attacks annually, you should know how useful your security training is at modifying human behavior, which is critical to improving training effectiveness.
Bring Manufacturing Back to America
Bringing research and manufacturing back to the U.S. is important to our economy and national security. Reshoring requires substantial capital and time, so government cooperation with industry is imperative.
What Are Blue Teams and Blue Team Exercises?
Blue teams are responsible for monitoring, detecting, and reacting to security threats. Click here to learn more about blue teams.