Phishing is a popular form of cybercrime because it is effective. Email provides direct access to you, and all successful email-based attacks are disruptive. Read and share these practical steps to reduce human error and loss events.
Category: IT Policies and Controls
The Cost of Capital After a Data Breach
Knowing that one data breach can influence your cost of capital, will you break trust with your customers and lenders? The uncertainty of future business and cash flow disruptions require evaluation.
Cyber Threats in Advanced Enterprise Manufacturing
Enterprise manufacturers are susceptible to cyber attacks. We will discuss some of the threats that advanced manufacturing faces today and precautions to ensure stakeholder expectations are maintained.
Work From Home Incident Protection
As more people access company resources from home, this shift creates many unexpected variables for manufacturers that may harm employees and the company. Learn more about these concerns within this article.
Cyber Security Policy: How to protect your business
Let’s explore how undocumented expectations cause human errors that impact your business and how to create a strong cyber security policy.
Intellectual Property Protections
The theft of vital or sensitive business secrets occurs daily. Protecting intellectual property should be one of your top priorities to ensure competitive advantage.
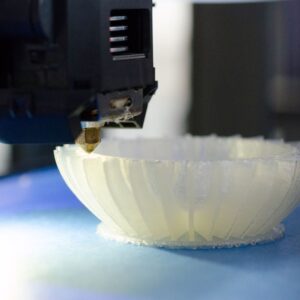
3D Printing in U.S. Manufacturing
3D printing or additive manufacturing has become popular in recent years, and many security experts have begun to express their concerns.
What is Social Engineering?
Given the financial losses due to the volume of social engineering attacks annually, you should know how useful your security training is at modifying human behavior, which is critical to improving training effectiveness.
What Are Red Teams and Why Conduct Exercises?
Valuable and objective insights about the existence of vulnerabilities, efficacy of defenses, and mitigating controls for the U.S. manufacturing industry. Click here to learn more about Red teams.
Backup Policy: What You Should Know About Backing Up Your Data?
Data loss and downtime not only impact budget, business interruption can tarnish reputations and sever relationships. Click here to find out why.