The theft of vital or sensitive business secrets occurs daily. Protecting intellectual property should be one of your top priorities to ensure competitive advantage.
Category: Security Frameworks
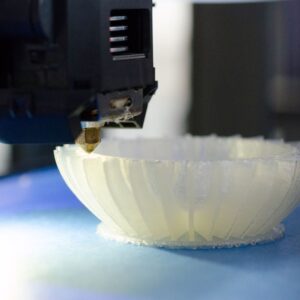
3D Printing in U.S. Manufacturing
3D printing or additive manufacturing has become popular in recent years, and many security experts have begun to express their concerns.
What is Social Engineering?
Given the financial losses due to the volume of social engineering attacks annually, you should know how useful your security training is at modifying human behavior, which is critical to improving training effectiveness.
15 Misconceptions About Supply Chain Cybersecurity
Comments or concerns regarding cybersecurity can often be myths or misconceptions. This article explains why inaccurate conclusions and misconceptions about cybersecurity are common contributors to disruption within supply chains.
Cybersecurity Maturity Model Certification (aka CMMC)
CMMC aims to become a verification mechanism for protecting Controlled Unclassified Information (CUI) and establishing cybersecurity controls on Defense Industrial Base (DIB).
Why Manufacturers Willingly Conduct Regular Cybersecurity Risk Assessments
Cybersecurity risk assessments have become a crucial part of any IT management strategy. Click here to find out why.
The risk of supply chain cybersecurity threats
Supply chains are a primary target for cyber-attackers, so how do manufacturers go about implementing protective measures to mitigate supply chain risk? Let’s find out.
Has the Perimeter Disappeared in Network Perimeter Security?
Companies have moved to multifaceted network architectures for layered security. What does that mean for perimeter security? Click here to find out.
What to Include in a Written IT Security Policy
Business leaders must reassess their information security requirements and management processes as modern cyber threats grow in frequency and sophistication. Many companies focus on integrating advanced cybersecurity tools and third-party services. However, it’s essential to recognize the vital role written IT security policies play in protecting digital assets and sensitive data. These guiding documents help…
Continue What to Include in a Written IT Security Policy
Why It’s Important to Have Information Security Standards
As companies worldwide continue to ramp up their data collection, storage, and analysis capabilities, the risk of large-scale cybersecurity incidents grows increasingly severe. Modern cyber criminals utilize various hacking techniques to gain access to critical infrastructure and sensitive data stores, capitalizing on network vulnerabilities, human error, and lackluster IT security frameworks. Organizations that take a…
Continue Why It’s Important to Have Information Security Standards