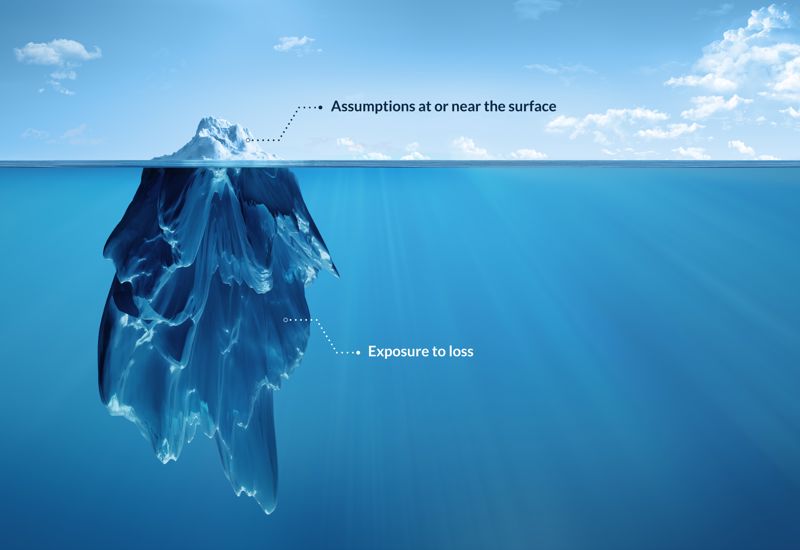
Does this sound familiar? They tell me we are secure, but I do not feel comfortable with the explanations. It’s fair to suspect that leaders using assumptions and facts from two or three years ago for cyber now face asset exposures disconnected from the reality of the risk they assumed when making investment decisions.
Threats have changed as your business integrated digital functions and work from home to streamline operations. The decision-making process no longer captures the exponential growth of cyber risk as loss exposure expands.
Leadership teams need better insights into the cyber risks they commit to cover. Due to low clarity and significant assumptions, the cyber risk decisions intended to prevent, in turn, cause disruption, stress, and loss. Cyber attacks, specifically ransomware attacks, are causing damage across supply chains and industries.
Limitations to Success
One of the biggest challenges in aligning budgets with asset protection is validating the prevention, detection, and response plans. You need a process that identifies gaps not covered by existing controls or personnel. Accurately aligning the effects of threats to your assets resulting in probable loss with facts, is complicated when every company has different exposures, risk tolerances, and critical assets.
Do you have a high tolerance for risk, and are your customers fine with shipment delays? Increased clarity is essential because executives and managers commonly under-evaluate loss prevention investments, let alone expenses in the response and recovery post-breach. There is a need for deeper shared understanding, insights, and documented outcomes over time.
The information translated through the ranks within the chain of command evolves with each person’s perspective and bias. A common occurrence is that this once actionable request for funding is so diluted that the objective for the request changes.
Scope creeps when a person or group crams more requirements into a project with the hope of receiving funding or when they desire to complete additional work at a reduced price. This effort often backfires because the deviations increase the budget and dilute the outcome for the business stakeholders.
Many daily breaches are due to unpatched software, device misconfigurations, internet-facing assets, and unauthorized software on corporate-owned devices. These problems hiding below the surface consistently rank among the top reasons for attack exploits. Why do these exploits occur so often when there are people within most companies aware of these liabilities?
Assumptions and Bias
Our assumptions and bias determine how we interpret information. Assumptions are a thing that is accepted as true or as certain to happen without proof. Bias is a personal and sometimes unreasoned judgment in favor of or against one thing, person, or group compared with another.
Our unique filters cloud meaning, leading to confusion when translating subject details. Shared understanding distills information to a standard truth, vital for effective communication.
 What do you mean our assets are compromised? Loss exposure is a reality.
What do you mean our assets are compromised? Loss exposure is a reality.Four Reasons for Loss Events
Highlighted below are four common reasons that lead to a high percentage of loss events for businesses.
Negligence:
This first problem relates to irresponsible decisions made by technology staff and outsourced IT companies. This recurring theme is customary across business sizes and industries. Some IT people and many network services companies are not managed effectively and will do enough to get by management’s radar. The absence of accountability allows unmotivated people and third parties to collect payments without performing the agreed-upon duties.
Usually, during a business disruption event, the leadership team discovers that their assumptions about business protection and recovery are incorrect. Instead of prioritizing recovery efforts, attention diverts to allocating capital to pay the ransom.
Unaware:
We also meet talented team members with networking or systems skills who quickly resolve workflow issues. The steps taken to address the computing issues lack good controls and security standards. The lack of security awareness cause increased exposure and harm to the business, as do other shortcuts taken each week.
You don’t know what you don’t know. Most people are open to making better decisions when they understand the ramifications of their actions.
Funding:
Funding continues to be a limitation, especially when a spending request accompanies each problem. During conversations with multiple stakeholders in a given business, typically 85% state concerns about systems and applications’ reliability, privacy, and security.
Most technology team members desire to perform and make good decisions. Some have loosely defined responsibilities, but management continues declining funding requests. Over time, some technical team members grow so frustrated and beaten down that they leave the company. Others stay and become less caring and negligent in their duties. I have heard the words, “Why even try?” many times.

Outdated beliefs and assumptions continue to cause disruption and loss.
Mindset:
The last challenge for this article is that mindset shapes reality. Do you feel the IT department or outsourced IT company owns your business risk associated with asset security? Do you believe your business is not a target because you store no sensitive information? These beliefs and assumptions continue to cause disruption and loss to stakeholders.
Focusing on assumptions and leaving the risk mitigation and post-incident recovery to the IT department means leaving your organization vulnerable to attack from gaps not understood and unfilled. Will your customers remain calm during your failed recovery?
Then there are the IT people with big egos who avoid review and feedback to the detriment of their growth and increased risk to the company. Some CIOs, CTOs, VPs, and Directors struggle with humility and feel anxious asking for help. Some of these leaders never overcame this challenge and ultimately lost their jobs. Others engage in token conversations with third parties to appease senior management and the board.
Remaining in an outdated mindset will leave your critical assets at risk and hinder your ability to recover from a breach quickly, if at all. Both of these outcomes impact your profits, reputation, and career.
Six Forms of Cyber Incident Loss
Public and private boards search for answers to determine the officers’ assigned responsibility and accountability for cyber risk.
- Productivity: Loss resulting from the inability to deliver products and services.
- Response: Loss associated with the costs of incident response and managing the event.
- Replacement: Loss that results from having to repair or replace capital assets.
- Competitive Advantage: Losses resulting from exposed IP and other competitive differentiators.
- Fines and Judgments: Fines and lawsuits levied for contractual, civil, or criminal actions.
- Reputation: Loss resulting from external stakeholders’ perspective of increased liability and decreased value.

Of course, our assets and workflows are secure.
The Time for Action is Now
The root cause of leadership inaction and frustration is investments not meeting expectations. The chaotic combination of assumptions, poor communication, misunderstandings, inattention, mismanagement, bias, and egos create a perfect surge to capsize your business vessel.
An engaged, proactive, and informed board and leadership team clearly understands their fiduciary role and the organization’s security roadmap is necessary to mitigate risk and combat today’s cyber threats. By correctly understanding how cyber risks can have a financial impact, prudent prevention measures can help stave off breaches and keep businesses safe, secure, and prosperous.
Streamlined Simplicity
Stakeholders demand better insights into the risks they commit to cover. Once leadership and IT management understand that we utilize a multi-stakeholder shared purpose approach, openness and interest improve. Why does knowledge of the process change engagement? Once business and IT management know that we focus on helping the team and not displacing them or harming their reputation, fears subside.
Without excuse, without pride, reach out to address the stress that keeps you awake at night. Once you reach a consensus on the workflows to be secured, we can combine our talents with less friction and waste to protect your value to your customers. Shared understanding is a force multiplier that allows for higher-value conversations, information, and actionable insights.
Improved decision-making awaits your action to transition from assumptions to shared understanding. We look forward to collaborating with you.
As a proud supporter of American companies, Certitude Security® is working diligently to inform leaders and facilitate essential asset protection priorities for manufacturers and supply chains throughout the United States.
Problem discussions can be a defining moment in your career. If you are interested in value creation, learn about SPOT-Beam™ by Certitude Security®. We look forward to helping you and your business succeed!

